What is token spoofing?

I was recently browsing Etherscan to get some examples of OtherDeeds metadata for a presentation when I noticed that Ethereum accounts holding these NFTs had received an ERC721 token from the “Primates” Collection. Taking a further look into the collection showed an enticing image which seems to fit with the broader Otherside metaverse style and narrative and so I went to check who had deployed the NFTs to see if they were officially connected to the project and could be a secret drop to holders before an official announcement.
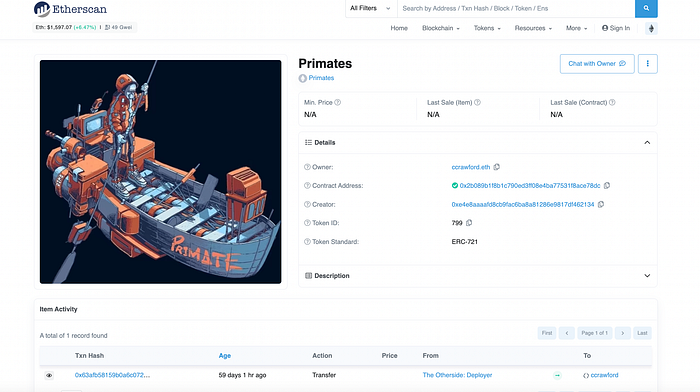
Etherscan’s transfer table showed that the sending contract is called “The Otherside: Deployer” and listed the contract as `0xe53c9cbfc1314b6cf6ba508230457df130552bc6`.
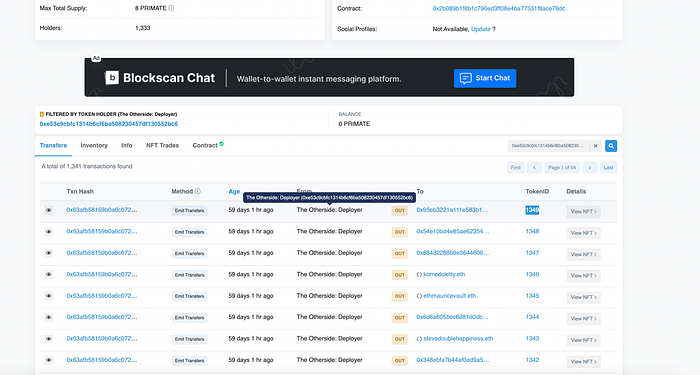
I then went onto the official contract for OtherDeeds (OTHR)
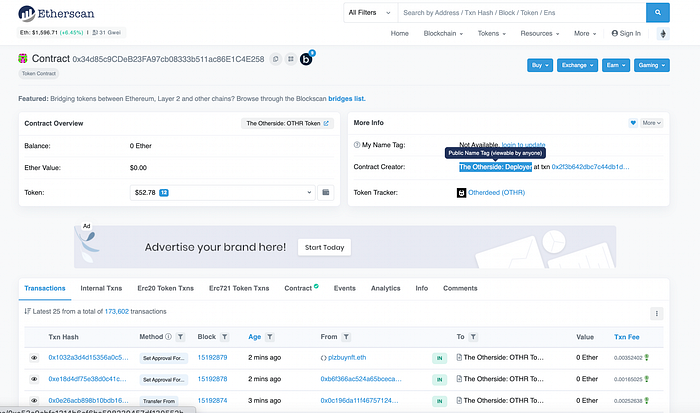
And clicked on the ‘Contract Creator’ account to double check. Sure enough this opened the contract ` 0xe53c9cbfc1314b6cf6ba508230457df130552bc6` . I checked the front 7 characters and back 7 to ensure this wasn’t a vanity address but boom, it was the exact same address.
https://tara-annison.medium.com/what-is-a-vanity-address-d689502a7800
How exciting, I’d found a yet to be announced Otherside metaverse NFT drop! Or had I ….
Well it turns out it actually isn’t and this is a practice called spoofing — where you create a token smart contract and then in the `transfer` or `transferFrom` event you list an arbitrary address, most effectively for a well known project or application. This will be picked up by block explorers and services who just show this data rather than the _actual_ sending account.
We can see this when we did into the the Primates contract:
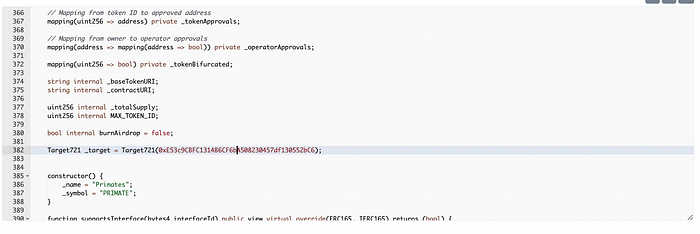
https://etherscan.io/address/0x2b089b1f8b1c790ed3ff08e4ba77531f8ace78dc#code
Here they have just added in the official Otherside: Deployer contract account so that it will show up in the transfer information even though it isn’t the real originator of the transaction.
Clever right!
So how can you avoid being duped by such a clever tactic?
If we take a transaction sending some Primate NFTs then we can see that the `from` address is clearly different from the Otherside: Deployer contract

However just to add some additional complexity into the mix, not all token transfers initiated by a different address are necessarily a spoofing event. Many dApps will send tokens in bulk from a different contract address and so you need to interrogate the transaction at hand and understand which of these is the more likely scenario.
Originally published at https://www.linkedin.com.
